About This Course
This course will be an advanced reverse engineering class for security researchers who want to expand their horizons and skills in reverse engineering C++ binaries.
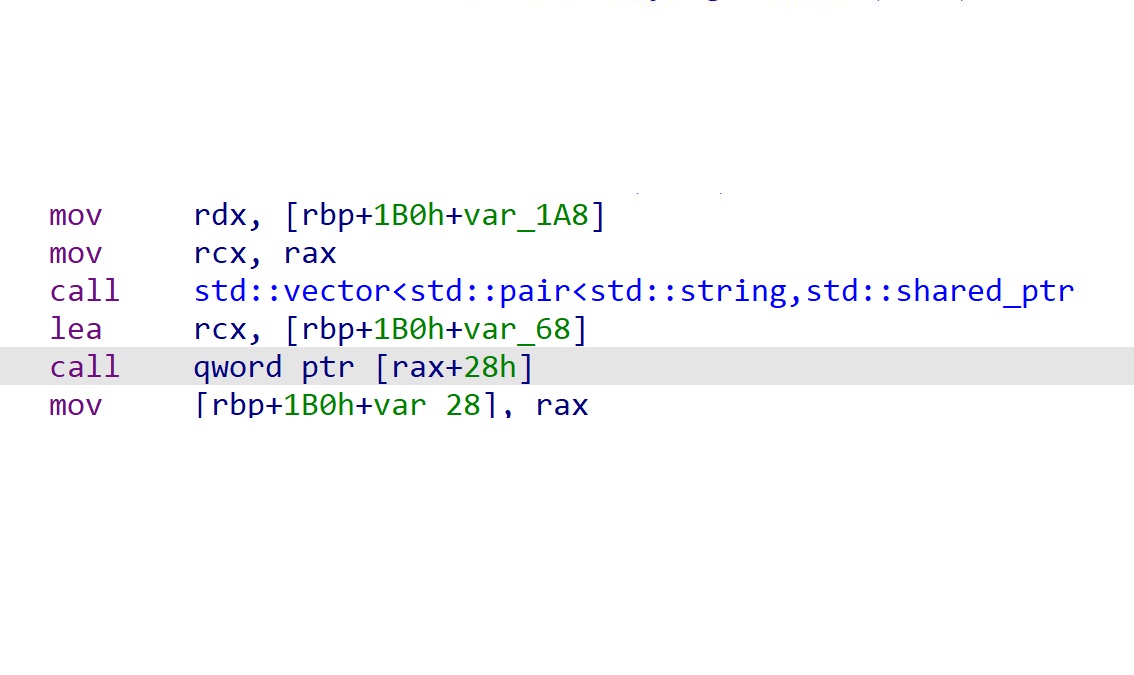
C++ Binaries are full of mysteries, they have objects, inheritance, templates, vtables and many more and reverse engineering them is a task on its own. In order to correctly and clearly map a C++ compiled binary it requires a vast knowledge of C++ Internals.
The training will explain C++ reverse engineering topics including techniques and tools for dealing with C++ Binaries research. We will start with the identification of basic structures in C++ and continue with C++ Objects and Inheritance in binaries and how to represent them in IDA. We will also study work methods and design patterns in C++, practice, fight and untangle deep and modern C++ programs using static and dynamic analysis.